Balancing Risk and Proactivity
A CISO's Guide to Effective Cybersecurity Strategy
Victor Monga
2/27/20232 min read

Maximizing Cybersecurity Success: The Power of CIS Controls and Benchmarks
As a CISO, it can be challenging to balance the need for proactive cybersecurity measures with the reality of managing risk.
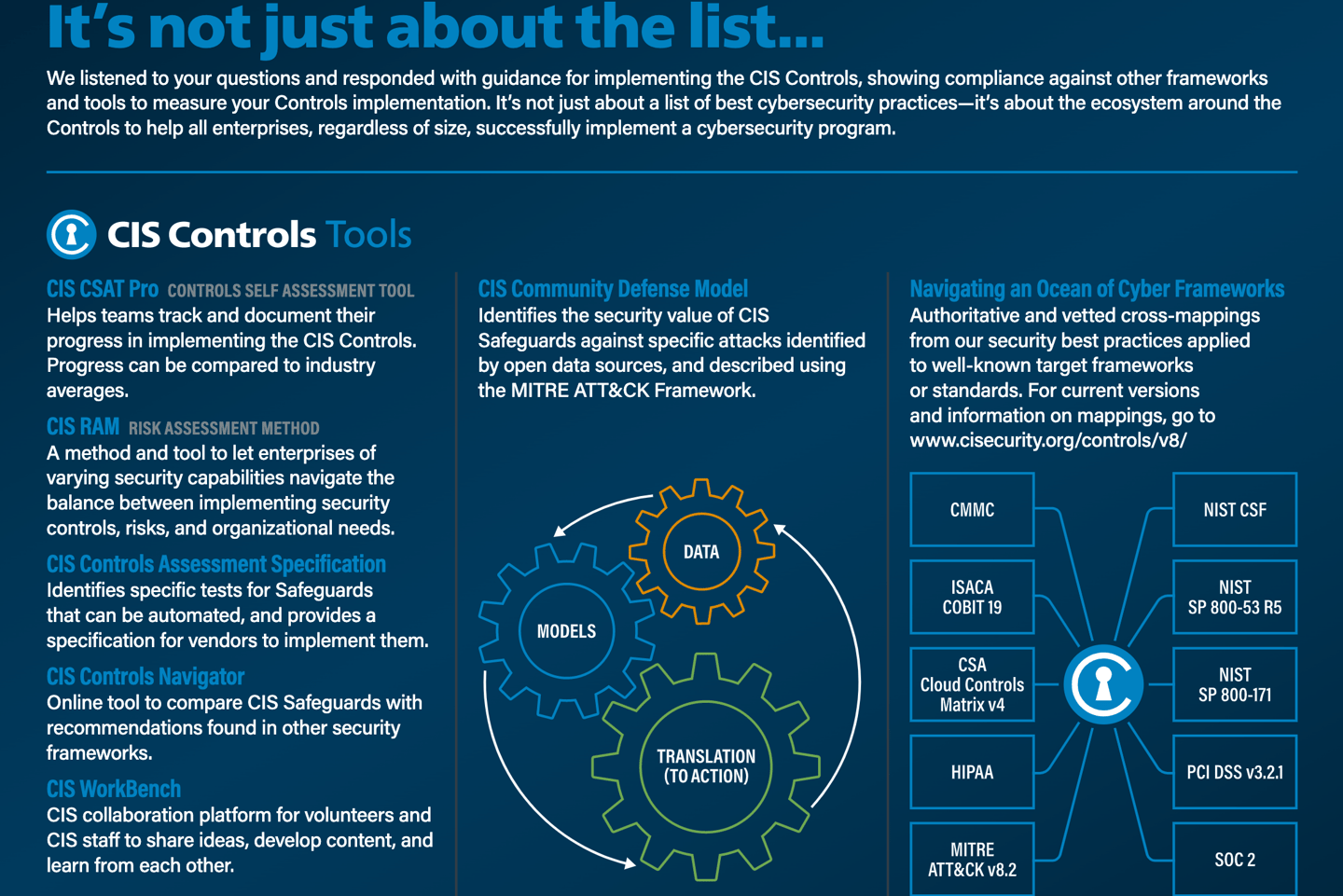
However, with the help of the Center for Internet Security (CIS), you can create an effective cybersecurity strategy that strikes the right balance. One of the key tools provided by CIS is their set of 20 critical security controls, which have been proven to reduce the risk of cyber attacks by up to 94%. By implementing these controls, you can improve your organization's security posture and better protect against cyber threats.
Implementing the 20 CSC: Insights and Challenges
A Cybersecurity Leader's Journey towards Bridging Security Framework and Operational Commands

In addition to the security controls, CIS also provides a set of benchmarks that can help you assess your organization's security posture and identify areas for improvement. By using the benchmarks to measure your organization's performance against industry standards, you can ensure that your cybersecurity strategy is up-to-date and effective.

"Using the CIS controls and benchmarks has been instrumental in helping us to identify and mitigate vulnerabilities in our network," says Frances S. James, CISO at Mitchell, Luettgen and Carroll. "We've been able to improve our security posture and reduce the risk of cyber attacks thanks to the guidance provided by CIS."
Another important aspect of an effective cybersecurity strategy is incident response planning. By having a plan in place to respond to cyber attacks, you can minimize the impact of an incident and quickly get your organization back up and running.
"CIS provides a framework for incident response planning that has been invaluable to our organization," says Oliver Eriksen, CISO at Paucek Group. "By following the framework, we've been able to respond quickly and effectively to cyber incidents, minimizing the damage to our organization."
In conclusion, an effective cybersecurity strategy requires a balance of proactive measures and risk management. With the help of CIS, you can implement the critical security controls, assess your organization's security posture with benchmarks, and create an incident response plan to ensure that you are prepared for any cyber threat.
As the threat landscape continues to evolve, it is essential to stay up-to-date with the latest best practices and guidance provided by organizations such as CIS.
Subscribe to latest announcements
Copyright © 2025 Virtually Testing. All rights reserved.